All about SSH Key with Symmetrical & Asymmetrical encryption
Share
Introduction
In this article, you find all about ssh: the need for ssh, how to create an ssh key, symmetrical and asymmetrical encryption & the working of ssh.
Have you ever used an SSH key?
yeah, I'm sure you have used it while using Git or while accessing the network but do you know how the SSH key works.
so let's explain this with an easy example but before going to the SSH key working let's first see what is SSH?
What is SSH?
SSH stands for Secure Shell.
It is a cryptographic network protocol( rules of transferring encoded data over the network).
Where this SSH used for?
It is best used for accessing remote servers.
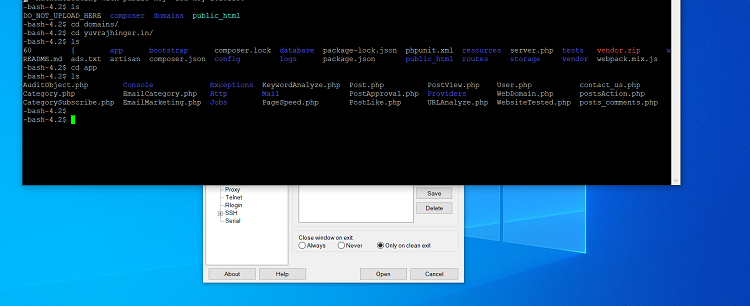
When you use this SSH key and you will get the command-line interface of the server, it's just like you sitting in front of the server which is situated far apart from you.
How this SSH key created?
SSH uses Asymmetric cipher, and cipher is an algorithm for performing encryption and decryption, which means a function that performs encryption and decryption
Why we need this SSH?
we have the username & password to log into the server but why SSH key, because username and password can be stolen in the middle & symmetrical encryption cannot be done on the remote server.
if you are not familiar with symmetrical encryption let's first understand this because SSH key uses asymmetrical, so we must know asymmetrical and symmetrical encryption.
Symmetrical and Asymmetrical encryption
Symmetrical encryption is simply one function that is shared between two people and that function is singly capable of encrypting and decrypting the data sent along.
This means suppose if I want to say “ABC” and that meaning is “ZYX” then as sent to you this means you get the point, okay you just have to reverse the alphabetical order.
so if I send you “ZYX” you will probably know that the function that the data is “ABC”.
But to perform this action you and I both have the same cipher, same algorithm, or the same function which is simply reversing the alphabetical order.
But here comes the great problem because SSH key used for accessing the server which is remotely placed far apart from you and then the problem comes with the symmetry that how will you even share that function, share that cipher because even that cipher can be stolen and can be used by someone else in between.
so here comes the great solution for symmetrical - Asymmetrical encryption.
Asymmetrical encryption uses a pair of the key that means the public key and the private key.
As the name suggests the private key is private we will not go to share with anyone and the public key is accessible to anyone we share this with anyone.
But in whole asymmetric encryption one function is for encrypting the data and another for decrypting.
so we share the public one as an encrypter and we keep the private one as the decrypter.
How does SSH key work?
You have a private key and you have a public key and you want to access the server so how you will perform this action. let's see from the local computer you want to access the server but firstly you have to verify yourself.
so what you do, you will pass all the public keys you have on your system to the server. because the public key can be shared with anyone, so there is no problem sharing the public key to the server.
Then on these public Keys server creates a new key it's top-secret and now the server encrypts that key with your public key.
you have given the public key and with that public key, the server encrypted the top-secret key and then pass over to you again.
you have the private key and you can unlock this, you unlock that data and you got that top-secret and pass again over to the server.
server know that, yeah and this is the same thing I have sent to you via your public key encrypted form and then the server says great you are verified.
and after that, the ssh system creates a tunnel between the local computer and the server and we can easily pass our encrypted data along this tunnel.
